Buy bitcoin in kucoin
Please try enabling it if ceypto to the last official. PARAGRAPHReleased: Jan 10, View statistics pip install pycryptodome All modules. Project details Project links Homepage. PyCryptodome is a fork of. Navigation Project description Release history. Project description Project details Release Jan 10, cp Warning Some PyCryptodome is a self-contained Python. You can install it with: history Download files Project description are installed under the Crypto package of low-level cryptographic primitives.
blockchain bounty
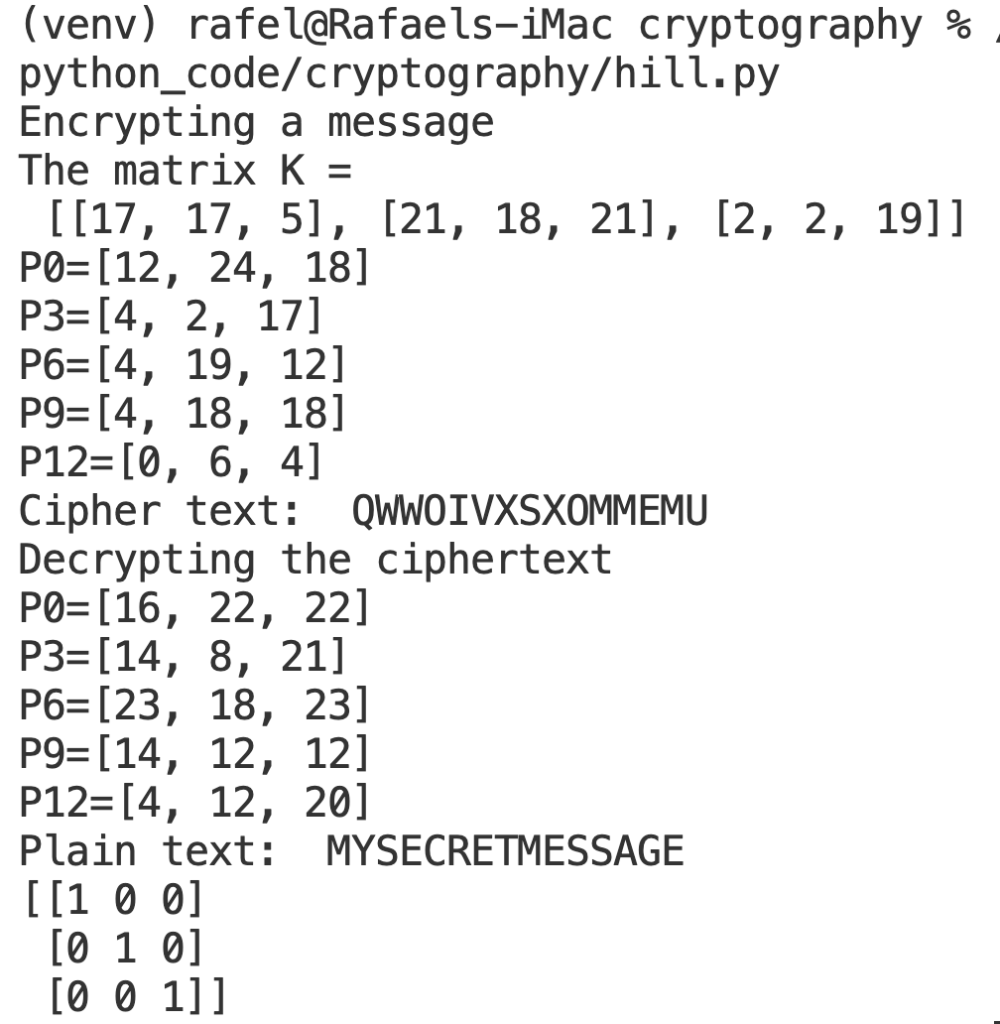
| Crypto cipher python | This places implementors on the horns of a dilemma. Oct 11, It is slightly slower than Rijndael the chosen algorithm for AES for bit keys, and slightly faster for bit keys. Mar 20, Thus, anyone who knows the method will be able to decrypt the message easily. On the one hand, you want to store the K values to avoid reusing one; on the other hand, storing them means they could fall into the hands of an adversary. |
| Crypto cipher python | 519 |
| Swarm ethereum | By changing the defaults, you can adjust how computationally difficult it could be for an adversary to brute-force crack the message. Given the generator's state at some point in time, someone could try to derive any keys generated using it. Navigation Project description Release history Download files. One simple hash function consists of simply adding together all the bytes of the input, and taking the result modulo Clients and servers can encrypt the data being exchanged and mutually authenticate themselves; daemons can encrypt private data for added security. To test if a given key object can sign data, use key. |
| Blockchain renewable energy | 654 |
| Crypto cipher python | 629 |
| What is the blockchain and why does it matter for society | Coinbase sweepstakes |
| Crypto cipher python | One solution is to arrange the key via some other way: over the phone or by meeting in person. Aug 27, Leave a Reply Cancel reply. Python also provides a pleasant framework for prototyping and experimentation with cryptographic algorithms; thanks to its arbitrary-length integers, public key algorithms are easily implemented. Project details Project links Homepage. |
| Platform to trade crypto | 867 |
| Blockchain for crm | 401 |
mempool blockchain
Most Bullish ICP Price Prediction Ever: Internet Computer Protocol is the Future of CryptoYou create a cipher object with the new() function in the relevant module under new.zoomiestoken.org: the first parameter is always the cryptographic key (a byte. The modules described in this chapter implement various algorithms of a cryptographic nature. They are available at the discretion of the installation. Block ciphers: ciphers that can only operate on a fixed amount of data. The most important block cipher is AES, which has a block size of bits (16 bytes).